Meet Flare September 25th, 2021 during the first edition of Bsides Montreal and don’t miss the conference of Olivier Michaud, AI expert at Flare, about ”Automatic Extraction of content from criminal underground forums.” … Read More
Digital Risk Protection

GoSec 2021 – Flare booth and conference
Meet Flare at its virtual booth September 22 and 23 during GoSec event. Don’t miss Yohan Trepanier Montpetit, our CPO speaking about Continuous Reconnaissance Approaches to Reduce External Risk. … Read More

Fireside Chat Video: The Role of the Dark Web in The Threat Landscape
Fireside Chat Replay: The Role of the Dark Web in The Canadian Threat Landscape With new threats raised by COVID-19, hybrid work, and the increased ransomware attacks we are seeing across the world, the threat landscape for companies today is … Read More

Noise Reduction and Prioritisation: One Size Does Not Fit All
Noise Reduction and Prioritisation: One Size Does Not Fit All One man’s trash is another man’s treasure, what one considers undesirable is likely specific to the listener. Or, at least, that is the unwritten rule in several situations, one of … Read More
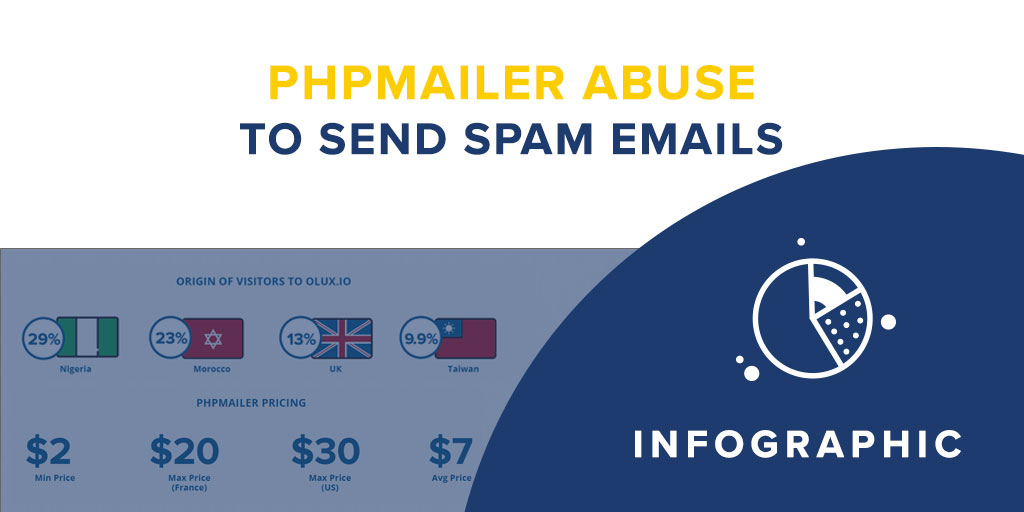
PHPMailer Abuse to Send Spam Emails
PHPMailer Abuse to Send Spam Emails PHPMailer Abuse to Send Spam Emails Spam ranks as a high threat vector for organizations. The PHPMailer library has been widely adopted in the criminal underground as a tool to send spam and monitor … Read More

Research Report: The Spam Email Business – A Comparison between Canada, USA, and France
The Spam Email Business: A Comparison between Canada, USA, and France RESEARCH REPORT Download the Report Executive Summary Despite the numerous sophisticated attack methods, spam still ranks as a high threat vector for organizations. According to the latest numbers, as … Read More

How to Mitigate the Risks of Token Leaks
How to Mitigate the Risks of Token Leaks Access tokens are used in token-based authentication and allow users to access a website, an application or API. After verifying their identity, the user has no need to re-enter their credentials for … Read More

How Prepared Are CISOs for Cloud Security Risks?
How Prepared Are CISOs for Cloud Security Risks? Since the COVID-19 pandemic started, remote teams have increased reliance on cloud communication and team collaboration services. Although there was interest in cloud adoption far before the pandemic hit, industry research has … Read More

Why your team should be concerned about leaky buckets on the internet
Why your team should be concerned about leaky buckets on the internet Since its inception in March 2006, AWS cloud storage option, also referred to as S3 (Simple Storage Service), has generated keen interest due to its low maintenance and … Read More

What kind of data could your PDF files be leaking online?
What kind of data could your PDF files be leaking online? In the 2003 timeframe leading up to the Iraq war, a British government representative published a Word document on their website, containing information related to “Iraq’s security and intelligence … Read More

